HBO Hack Underscores the Growing Threat of Digital IP Theft

HBO Hack Targeted Valuable Intellectual Property and Company Secrets
Corporate espionage and the theft of intellectual property and company secrets have gone cyber. The latest victim is cable network HBO and its flagship series Game of Thrones. The HBO hack, perpetrated by a hacker or group calling themselves “Mr. Smith,” may involve as much as 1.5TB of data. Mr. Smith has been releasing their treasure trove in increments; so far, they’ve leaked five Game of Thrones draft scripts, complete unaired episodes of Curb Your Enthusiasm and several other HBO series (although not GoT), the personal contact information of several GoT actors, company emails from HBO’s vice president of film programming, login credentials for HBO’s internal systems, and numerous other confidential documents.

The HBO hack has been compared to the 2014 Sony Pictures hack, which involved the release of scandalous company emails. However, there are more similarities to the Netflix hack in April, where hackers stole upcoming episodes of Netflix’s smash hit Orange is the New Black and dumped them online after Netflix refused to pay a ransom.
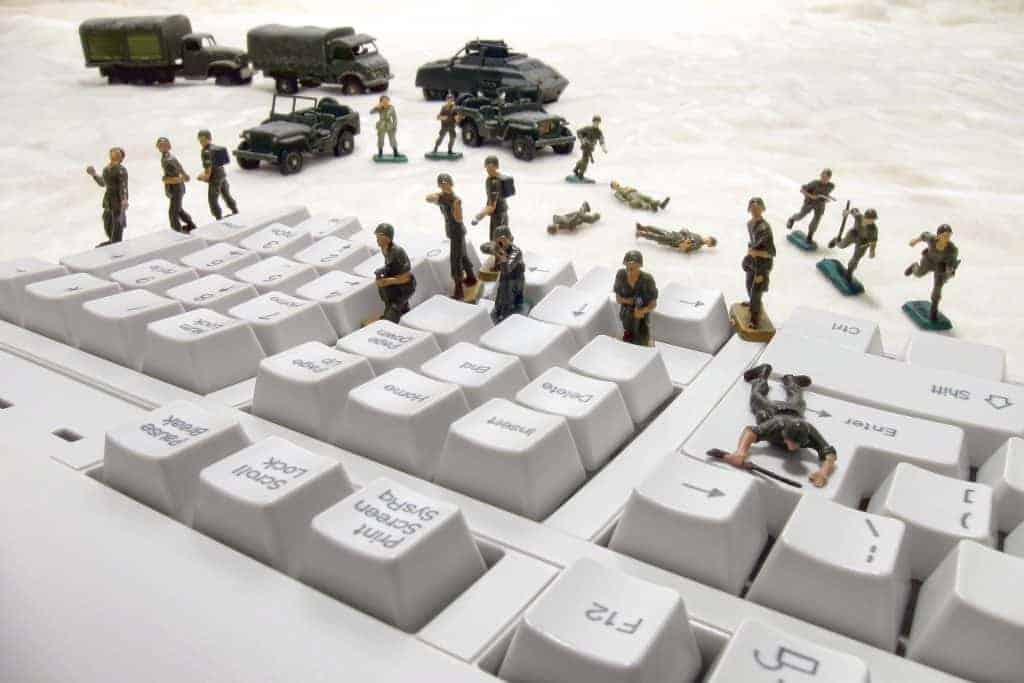
Hackers are Coming
The latest Verizon data breach report highlighted cyberespionage and digital IP theft as growing threats. The manufacturing industry, professional services, education, and the public sector were noted as being especially vulnerable, but any industry could be victimized.
Hackers are still very interested in stealing identities and payment card data, but there’s arguably even bigger money in stealing digital intellectual property. Mr. Smith is threatening to release more data from the HBO hack – including full GoT episodes – unless the network pays them six months’ worth of the $12 to $15 million they claim to earn annually from cyber crime. HBO has offered Mr. Smith $250,000 as a “bug bounty” payment, which Mr. Smith has scoffed at.
Lessons from the HBO Hack
Entertainment companies make particularly attractive targets for three primary reasons, all of which also apply to organizations far removed from the Hollywood spotlight.
The entertainment industry’s entire business model is built around intellectual property. Hollywood sells nothing but content, and they are always making more of it. The same applies to software, game, and web development companies, as well as any business that sells content as opposed to widgets. Even companies that don’t actually sell intellectual property are in possession of some: Think secret sauces, R&D data, product prototypes, proprietary software packages, and vendor and customer lists. The Houston Astros MLB team lost millions of dollars when a competing team hacked their database and stole information on potential prospects and trades.
The industry is going digital. Film cans are being replaced by hard drives, consumers have come to expect online streaming options, and everything that’s ancillary to productions, such as scripts, lists of shooting locations, and actors’ personal information, is stored on networks. As organizations move from storing records in file cabinets to storing them on hard drives and in the cloud, hackers have more access points to more digital IP and company secrets than ever before.
The typical Hollywood studio has a complex cyber ecosystem. Film and TV studios depend on numerous third-party vendors to perform services, from sound dubbing to film editing, that involve access to company data. Often, these businesses are small and do not have the same level of cyber security as major studios. The Netflix hack was traced back to a breach at a small, third-party vendor – as was the latest Anthem breach and other recent breaches impacting Google, Trump Hotels, and Verizon. Outsourcing IT services to third-party vendors is commonplace in the digital age, so it is critical for all organizations to secure their entire cyber ecosystem, including business associates who have access to company data.
Hackers will keep engaging in digital IP theft because it’s lucrative. Companies will pay big bucks to protect their intellectual property and trade secrets. It’s far less expensive to invest in proactive cyber security and prevent IP theft from happening in the first place.
The cyber security experts at Continuum GRC have deep knowledge of the cyber security field, are continually monitoring the latest information security threats, and are committed to protecting your organization from security breaches. Continuum GRC offers full-service and in-house risk assessment and risk management subscriptions, and we help companies all around the world sustain proactive cyber security programs.
Continuum GRC is proactive cyber security®. Call 1-888-896-6207 to discuss your organization’s cyber security needs and find out how we can help your organization protect its systems and ensure compliance with all applicable laws, frameworks, and standards.
[bpscheduler_booking_form]